The assumption that your private residence remains a sanctuary is often a dangerous fallacy. In 2023, the global market for surveillance technology expanded by 12.5 percent, placing professional-grade monitoring tools in the hands of almost anyone with a grievance or an agenda. For the principal, the threat isn't just a possibility; it's a persistent operational reality. True counter surveillance isn't found in a retail gadget or a basic sweep. It's a technical discipline forged in the high-stakes environments of the Royal Marines and specialist police units. Service. Discretion. Protection.
You understand that your private conversations are your most valuable currency, and the thought of them being leaked is unacceptable. We agree that off-the-shelf solutions offer little more than a false sense of security. This article details the elite methodologies and technical counter-measures used to secure the privacy of high-net-worth individuals against sophisticated monitoring. We'll explore how professional sweeps, signal analysis, and lifestyle integration provide total privacy within your residence and vehicle. This is the invisible support structure that allows you to live without concern. The people behind the principal, ensuring your world remains your own.
Key Takeaways
- Understand why modern counter surveillance requires a proactive, strategic approach to identify and neutralise sophisticated monitoring before it compromises your privacy.
- Learn the methodology behind professional TSCM surveys, moving beyond basic electronic sweeps to achieve the elite standard of technical and spectral analysis.
- Recognise the critical security gaps left by consumer-grade hardware and the necessity of professional-grade equipment in high-stakes environments.
- Master the "Discretion Protocol" to identify subtle signs of compromise and take immediate, disciplined action if you suspect unauthorised monitoring.
- Discover how technical security measures integrate seamlessly with elite Close Protection to provide a comprehensive, invisible shield around the principal’s lifestyle.
Beyond the Hardware: Defining Modern Counter Surveillance
True privacy requires more than high walls and gated entries. It demands a proactive, tactical posture. To understand What is Counter Surveillance?, one must look beyond the hardware. It is the discipline of detecting, neutralizing, and preventing unauthorized monitoring. In 2026, the methodology of the adversary has shifted. It's no longer just about the lens; it's about the data stream. We define counter surveillance as the active measures taken to ensure your private life remains exactly that.
UHNW individuals are primary targets for sophisticated actors because information is a high-value currency. Whether the motive is corporate leverage or personal intrusion, the methods are increasingly professional. There's a vital distinction between passive protection and active counter-measures. Passive protection is a lock on a door. Active counter-measures involve a systematic sweep of the radio frequency spectrum and physical environment to find what shouldn't be there. For these measures to be effective, they must remain invisible. Discretion is our primary tool. If an adversary knows they're being hunted, they simply go dark and wait. We ensure they never get the chance.
The Evolution of the Threat Landscape
The threat has moved from simple audio bugs to advanced GSM and Wi-Fi-based eavesdropping. In 2024, data showed a 22% increase in the use of "near-field" digital implants that piggyback on existing smart home infrastructure. These devices don't just listen; they transmit. Most traditional security companies miss these nuances because they think in terms of locks and bolts. They don't have the technical depth to manage high-level espionage. Digital surveillance now intersects directly with physical privacy. A breach in your network is a breach of your bedroom. You need specialists who understand the signal, not just the sensor.
Privacy as a Strategic Asset
Privacy isn't a luxury. It's a necessity for personal safety and reputational integrity. A surveillance breach is often the precursor to a physical security risk. It allows an adversary to map a principal's pattern of life, identifying vulnerabilities before they ever set foot on the property. Our approach at Black Key London is built on a foundation of elite service. We aren't a security company. We are the people behind the principal. This philosophy ensures total silence and integrated protection. Derived from years of service in the Royal Marines and specialist police units, our standards are forged in high-stakes environments. We provide the invisible support structure that allows you to live without concern. Service. Discretion. Protection.
Technical Surveillance Counter-Measures (TSCM): The Elite Standard
TSCM is the gold standard for a reason. It is a systematic, highly disciplined process of detecting and nullifying electronic eavesdropping devices. For the principal, it represents the difference between a private home and a public stage. A professional survey is not a cursory glance with a handheld scanner. It is a multi-layered methodology involving physical, technical, and spectral analysis. This standard is forged from years of operational experience where the stakes are absolute.
When acquiring a new residence, a baseline sweep is mandatory. Pre-existing vulnerabilities or legacy systems can compromise a family's privacy before they even move in. Regular, scheduled sweeps are equally vital. Threats evolve. Technology changes. A "clean" environment today requires constant vigilance to remain so tomorrow. It's about maintaining a sterile environment through methodical repetition and technical excellence.
The Components of a Professional Sweep
A professional sweep utilizes sophisticated hardware that goes far beyond consumer-grade detectors. Our approach involves three core technical pillars:
- Radio Frequency (RF) Analysis: This detects active transmissions. We scan the entire spectrum to identify unauthorized signals, from low-frequency bugs to advanced burst transmitters that hide in plain sight.
- Non-Linear Junction Detection (NLJD): Essential for finding dormant electronics. This technology detects the semiconductor components within devices, even if they're powered down or hard-wired into the structure of the building.
- Thermal Imaging: Hidden power sources generate heat. High-resolution thermal cameras can identify a 0.1-degree Celsius temperature variance, revealing devices concealed behind drywall or within bespoke furniture.
Securing the Digital Perimeter
Privacy extends beyond the physical walls. The digital landscape is often the most vulnerable entry point for modern intrusions. We analyze Wi-Fi networks for unauthorized access points or "man-in-the-middle" configurations that could intercept sensitive data. A secure home must have a secure network; one cannot exist without the other.
Mobile assets require the same level of scrutiny. Hidden GPS trackers on vehicles are a common method for monitoring a principal's movements. Our team conducts thorough physical and electronic inspections of all transport assets to ensure no tracking devices are present. Implementing secure communication protocols is the final layer. It prevents remote surveillance from gaining a foothold. For those who value absolute privacy, our bespoke counter surveillance protocols provide the necessary peace of mind. True security is silent. It's a foundation of trust built on technical excellence and the quiet gravity of expertise.
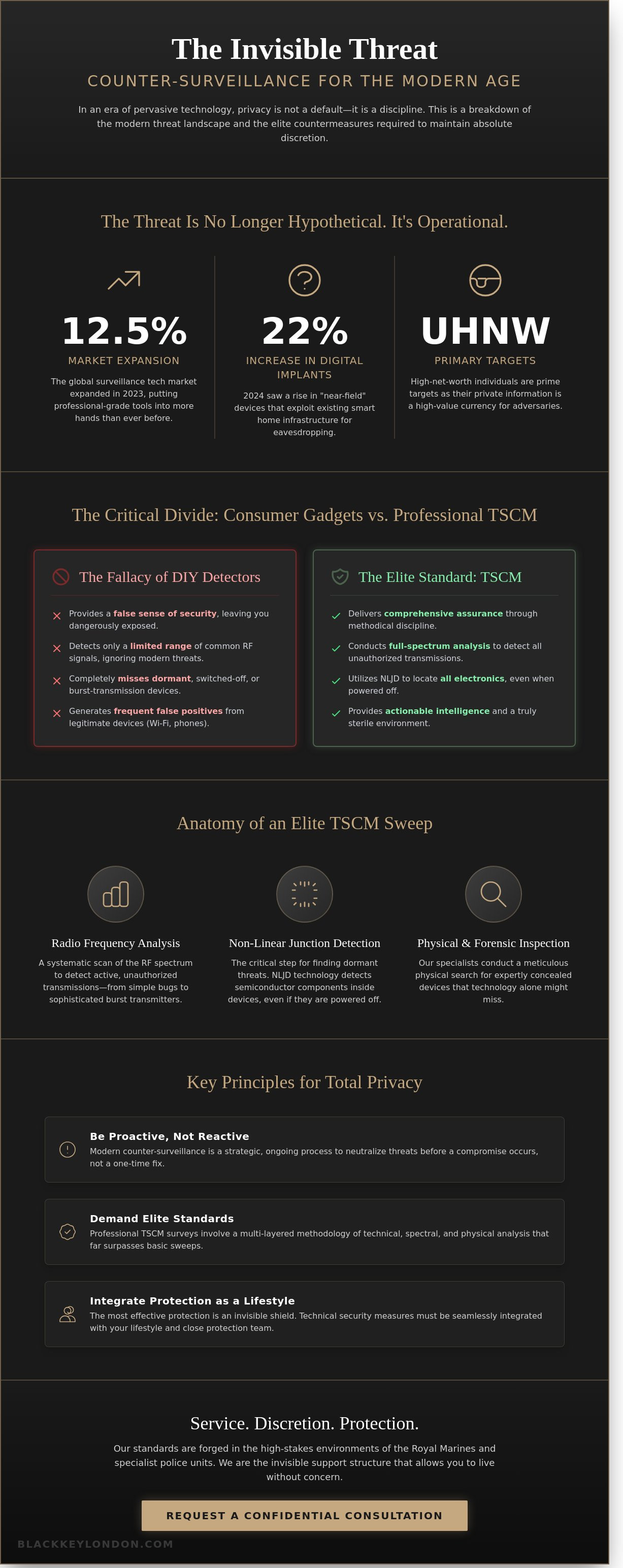
The Fallacy of DIY Bug Detectors vs. Professional Sweeps
Real security isn't found on a retail shelf. Many principals believe a £200 plastic wand purchased from an online marketplace provides a shield against intrusion. It doesn't. These devices offer an illusion of safety that is often more dangerous than having no protection at all. Relying on consumer-grade hardware for counter surveillance creates a false sense of security, leaving the residence vulnerable to sophisticated threats that remain undetected.
Professional bugging devices are designed to bypass basic detection. A cheap wand might beep at a microwave or a Wi-Fi router, but it will remain silent when faced with a high-end transmitter. True protection requires a level of technical sophistication and tactical experience that off-the-shelf products cannot replicate. Service. Discretion. Protection. These are not achieved through gadgets, but through rigorous operational standards.
Why Consumer Hardware Fails
Consumer detectors lack the processing power to identify modern threats. Professional-grade bugs often use "burst" transmissions, where data is compressed and sent in a fraction of a second, sometimes less than 100 milliseconds. A basic detector simply isn't fast enough to catch these spikes. Modern residences are also saturated with signals. A typical UHNWI home may have 40 or more connected IoT devices, creating a "noisy" environment. Basic hardware cannot distinguish between a legitimate smart home signal and a frequency-hopping bug. This leads to constant false positives that mask real threats. These tools lack the sensitivity to find "dark" or dormant bugs that are professionally shielded or programmed to activate only at specific times.
The Human Element: Expertise Over Electronics
The equipment is only as effective as the person operating it. Our methodology is forged in the Royal Marines and specialist police units. We don't just rely on electronics; we rely on an operational mindset. We are not a security company in the traditional sense. We are the people behind the principal, providing a bespoke service that views counter surveillance as a forensic process.
Our specialists understand the "attacker mindset." We know where a professional would hide a device, whether it's inside a hard-wired electrical fitting or embedded within the structural fabric of a room. We interpret complex spectral data that automated tools ignore, identifying anomalies in the radio frequency environment that suggest a breach. A machine can show a graph; an expert sees a footprint. This combination of high-end spectrum analysis and a physical, tactical search is what ensures total privacy.
- Tactical Experience: Backgrounds in elite military and police units inform every search.
- Spectral Analysis: Identifying signals in the 0Hz to 24GHz range that consumer tools miss.
- Physical Rigour: A forensic examination of the environment that goes beyond the digital.
Operational Discretion: Identifying and Mitigating Surveillance Risks
Vigilance is a quiet discipline. It isn't about paranoia; it's about the clinical observation of your environment. For the UHNWI, the home is a sanctuary that must remain impenetrable. When that perimeter is breached, the signs are often microscopic. Effective counter surveillance begins with the principal's ability to spot these anomalies without alerting a potential adversary. This requires a shift in mindset. You must become a passive observer of your own space.
Red Flags and Indicators of Compromise
Technical surveillance leaves footprints. You might notice unexplained interference on your landline or a subtle clicking during mobile calls. Electronic devices might exhibit faster battery depletion or unexpected data spikes. These are technical echoes of a breach. Physical signs are equally telling. Look for a fine layer of white dust on a sideboard, suggesting a wall has been drilled. Furniture moved by even two centimeters can indicate someone accessed a floor box or a power outlet. A 2022 security industry report indicated that 45% of technical devices are discovered through these simple visual discrepancies.
The human element remains your greatest vulnerability. Internal data suggests that over 60% of domestic security breaches involve an "insider threat" or a poorly vetted contractor. This is why rigorous domestic staff vetting is the foundation of any protective strategy. A new face in a maintenance crew or a long-term staff member with sudden, unexplained lifestyle changes warrants a discreet review. The people behind the principal must be as vetted as the technology protecting them.
The Protocol for Suspected Breaches
If you suspect your privacy is compromised, your reaction must be immediate and invisible. Emotional responses lead to tactical errors. Follow this operational protocol to regain control.
- Step 1: Maintain Total Silence. Don't discuss your suspicions inside the residence. Assume every room is "hot." Continue your daily routine exactly as before. If you stop talking about sensitive business, the observer knows they've been spotted.
- Step 2: Secure Communication. Leave the property. Use a secure, external location to contact your professional team. Use a device that hasn't been inside the residence.
- Step 3: The Maintenance Guise. We don't arrive in marked vans. A professional counter surveillance sweep is conducted under the cover of a routine service, such as an HVAC inspection or an IT upgrade. This prevents the observer from "going dark" or remotely wiping evidence before it can be collected.
Maintaining a facade of normalcy is vital. If an adversary realizes they've been detected, they'll often retreat and adapt, making them harder to catch later. We provide the expertise to identify the threat while you maintain the rhythm of your life. Service. Discretion. Protection.
Integrated Protection: Surveillance Mitigation as a Lifestyle Standard
Security isn't an accessory. It's a foundation. For the modern principal, true safety requires more than physical barriers; it demands the total control of information. We don't view counter surveillance as a reactive measure. Instead, we treat it as an essential component of a sophisticated lifestyle. Every engagement begins with a comprehensive Security Risk Assessment. This process identifies technical vulnerabilities that standard security firms often overlook. Data from 2023 industry security audits indicates that 64% of high-profile residences possess at least one undetected technical vulnerability in their home office or master suite. We close these gaps before they become liabilities.
The Residential Security Integration
We integrate technical sweeps directly into our Residential Security Teams. This creates a seamless shield. Our officers don't just watch the perimeter. They monitor the RF environment as a standard part of estate management. This ensures that the only people with access to your private conversations are the people behind the principal. We maintain a clean environment through constant vigilance. It's a tactical approach forged in the Royal Marines and refined for the private sector. We offer more than a service; we offer a promise of total privacy. One trusted team. One standard of excellence.
- Real-time RF spectrum analysis to detect unauthorized transmissions.
- Continuous monitoring of Wi-Fi networks for rogue access points.
- Vetting of all third-party contractors entering the inner sanctum.
Securing Global Travel and Logistics
Privacy shouldn't end at your front door. Our protection follows you across borders. We provide mobile TSCM sweeps for hotel suites, private aircraft, and temporary meeting rooms. Travel logistics are a primary point of failure in many security plans. We ensure your movements remain untracked. Our specialists arrive ahead of the principal to sanitize every environment. This proactive stance prevents the installation of tracking devices or listening posts. It's about maintaining the initiative. Service. Discretion. Protection. These aren't just words. They're the pillars of our operational philosophy. We provide the invisible support structure that allows you to live without concern. Counter surveillance is the quiet gravity of our expertise in action. We don't need to shout to be heard. We simply ensure that no one else is listening.
Protecting Your Private Horizon
True privacy isn't found in a retail gadget or a part-time security guard. It's built through rigorous standards and professional Technical Surveillance Counter-Measures (TSCM). This elite standard provides a level of certainty that consumer-grade hardware simply cannot match. For the UHNW principal, effective counter surveillance is an ongoing discipline rather than a one-off event. It requires a seamless integration of operational discretion into the rhythms of a global lifestyle. Security must be invisible; it must be absolute.
Black Key London was founded by former members of the Royal Marines and UK Police. This heritage ensures that our methodology is rooted in real-world operational success. We specialize in UHNW lifestyle and security integration, acting as the silent support structure for the world's most discerning individuals. Total discretion is our foundational service standard. We focus on the people behind the principal, translating elite military discipline into a refined, bespoke service. You deserve a partner who understands that high-stakes environments require composed, reassuring expertise. Your safety is our mission. Your privacy is our priority.
Take the first step toward reclaiming your peace of mind. Secure your privacy with a confidential consultation today. We're ready to stand watch.
Frequently Asked Questions
What is the difference between surveillance and counter surveillance?
Surveillance is the act of monitoring a target, while counter surveillance involves the active measures taken to detect and neutralise that monitoring. Surveillance seeks to gather intelligence without consent. Counter surveillance protects the principal's privacy by identifying vulnerabilities and removing illicit devices. It's a proactive defense. Our methodology, forged in the Royal Marines, focuses on the tactical detection of intrusive technology to ensure total operational security.
How often should a professional TSCM sweep be conducted?
A professional TSCM sweep should be conducted at least twice per year or following high-profile events. For UHNWIs, quarterly inspections are the industry standard for maintaining a sterile environment. Specific triggers include the arrival of new domestic staff or the conclusion of major renovations. Regularity ensures that any new threats are identified within a 90 day window. Consistency is the foundation of discretion.
Can professional counter-surveillance teams find hidden cameras that are not connected to Wi-Fi?
Yes, professional teams use Non-Linear Junction Detectors to find electronic components even if they're powered down or not connected to a network. These tools detect the semi-conductor junctions present in all modern circuitry. We also employ thermal imaging to locate the 1 or 2 degrees of heat signature emitted by active internal components. It's an exhaustive, physical and technical process. We leave nothing to chance.
Is it legal to use counter-surveillance equipment in the UK?
It's legal to use equipment for the protection of your own private property and data. However, the use of certain "jammers" that interfere with public telecommunications is restricted under the Wireless Telegraphy Act 2006. Our operatives ensure all sweeps comply with UK privacy laws and the Investigatory Powers Act 2016. Protection must always remain within the framework of the law. Excellence requires strict adherence to regulation.
What should I do if I find a listening device in my home?
You should immediately leave the room and contact your security lead from a separate, secure location. Don't touch or attempt to disable the device. Handling it can destroy forensic evidence or alert the adversary that they've been compromised. We recommend a 100 percent "hands-off" policy until a specialist team can document the find and conduct a full sweep of the perimeter. Silence is your best asset.
How long does a professional technical sweep of a large estate take?
A comprehensive technical sweep of a 10,000 square foot estate typically requires 12 to 16 hours of operational time. This duration allows for a methodical physical inspection alongside electronic spectrum analysis. We don't rush. Every inch of the principal's residence is vetted, from the HVAC ducts to the internal wiring. Precision takes time. Quality demands a steady, tactical pace and a focused mind.
Does counter surveillance include protecting my mobile phone and laptop?
Counter surveillance naturally extends to your digital life, as mobile devices are the most common entry points for modern eavesdropping. We implement encrypted communication protocols and conduct audits of device permissions to stop data exfiltration. This integrated approach ensures that your digital footprint is as secure as your physical residence. Protection is a 360 degree commitment. One relationship covers every potential vulnerability.
Why should I hire ex-military or police personnel for counter surveillance?
Ex-military and police personnel bring a level of operational discipline and "battle-hardened" reliability that civilian agencies cannot replicate. Their training in the Royal Marines or specialist units provides a unique perspective on threat detection and risk mitigation. They understand the gravity of the mission. They are the people behind the principal, offering a bespoke service built on a foundation of absolute integrity and elite standards.


